Networking at LTH
4 minute read
I recently started hosting more services on my home server, being careful to avoid direct port forwarding as to not make my IP visible on the internet. I thought how other students might not take the same kinds of precautions, and wanted to map out the local IP space in case anyone had interesting websites waiting to be discovered.
Tools Used
- Python: The primary programming language
- SQLite: For storing data easily
- LanceDB: For storing the image vectors
- OpenCLIP: For generating image embeddings
- Playwright: For taking JS page screenshots
- FastAPI: For hosting the backend
Method
Overview
Have you ever seen an IP geolocation tool and wondered how they work? There are a few ways they populate this data, but the most basic one is by looking at the WHOIS data and seeing the address:
❯ whois 55.67.89.10
OrgName: United States Department of Defense (DoD)
OrgId: USDDD
Address: 3990 E. Broad Street
City: Columbus
StateProv: OH
PostalCode: 43218
Country: US
RegDate: 2007-01-12
Updated: 2025-03-13
Ref: https://rdap.arin.net/registry/entity/USDDD
Because we want to find all IP addresses of students in Lund, we have the reverse problem: Finding all IP addresses given a location. The way I did this was by knowing that AF-bostäder uses Bredband2 for everyone's apartments, and looking up their ASN (AS29518). From here we can get a list of all IPv4 ranges from the ASN.
To filter out the ranges that are actually in Lund we use some heuristics (reverse DNS on the IP addresses and looking for Lund related items), and using DNS for finding the IP of known Lund servers (like afbostader.se). Once I had knowledge of one of the IP addresses in the block being inside of Lund, I just assumed that all of them would be in Lund (which is not at all guaranteed, but worked somewhat well).
Here are the ranges I found in the end:
LUND_IP_RANGES = [
"83.233.0.0/16",
"83.209.0.0/16",
"89.233.192.0/18",
"89.160.0.0/17",
"88.129.0.0/16",
"87.96.128.0/17",
"94.255.128.0/17",
"82.209.128.0/18",
"85.8.0.0/18",
]
Scanning the Network
Once I had the IP ranges we could start with the initial scan. I chose to split the scans in several "layers" as to avoid making too much noise on the internet (take note botnets):
- ICMP ping sweep
- TCP port scan (Port: 80, 443, 8080, 8443)
- Full website download + render
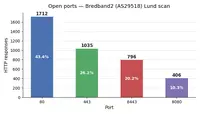
With each step I would reduce the potential candidates further, going from 300k+ to ~1700. Results were stored in SQLite for easy lookup.
CAUTION: Scanning networks like this is legal (at least in Sweden), but might break your ISP's ToS. Be careful when doing such scans. My internet connection actually stopped working as the scan was almost finished, leading me to suspect an ISP ban of my IP. Turns out it was just my VPN flagging me, and turning it off would re-enable internet access again :)
Rendering and Searching Images
I would screenshot all of the websites using Playwright (with the .screenshot() method). I just stored them in the filesystem under a single large folder that I could easily look through later for any interesting results.
Turns out 1700 images is a lot, so I wanted to cluster them in some way for better identifying similar images (and enabling semantic search).
I chose to vectorize them using OpenCLIP, and store the results in LanceDB for quick lookups. I then looked up image clustering algorithms and found HDBSCAN which supposedly works better than K-means clustering when the number of clusters is unknown (as in this case).
Result
There were quite a few websites that surprised me. A lot of them were just publicly accessible routers with password protection, while others were misconfigured web servers without any meaningful content. I presume these were accidentally set up back in the days.
Some websites were interesting however, and here are a few of my favorites:










I also found a surprising amount of misconfigured routers, giving others free access to:
- Reboot
- Change SSID name
- Change passwords
- See device metadata
- Upload custom router software (basically RCE)
And most interestingly for me I found my old corridor mate's website, that had not been updated for a while. I had no clue he had a website, but the whole point of this project was to find other engineers "secret" websites in this way. Given that goal I would say this project was a success, even though I found fewer self-hosted pages than initially expected.

I made the website accessible (with images!) if anyone wants to check it out: networking-at-lth.heimdal.dev
Note: This scan is a snapshot of the IP blocks on 2026-03-10. They might show no/different content than the images suggest when trying to connect to these addresses in the future. Use the website responsibly, it is illegal to take control of remote devices, even if doing so is trivial.